For local and remote monitoring within the same domain, the user who runs the AimBetter Agent service can have minimal permissions, as detailed in this document.
For remote monitoring within the same workgroup (different domain), the user must be defined as an administrator and have the same name and password in both the Agent and Monitored Servers.
1. Create and Set up the User Group (Domain User Required for Remote Monitoring)
- Creating a Domain User (For Remote monitoring, a domain user is required. You can use an existing user or create a new one.):
- On the Active Directory (domain), create a new domain user (e.g.,
DOMAIN\AimBetterUser) with a strong password. - Configure it so password never expires and user does not have to change password at next logon.
- On the Active Directory (domain), create a new domain user (e.g.,
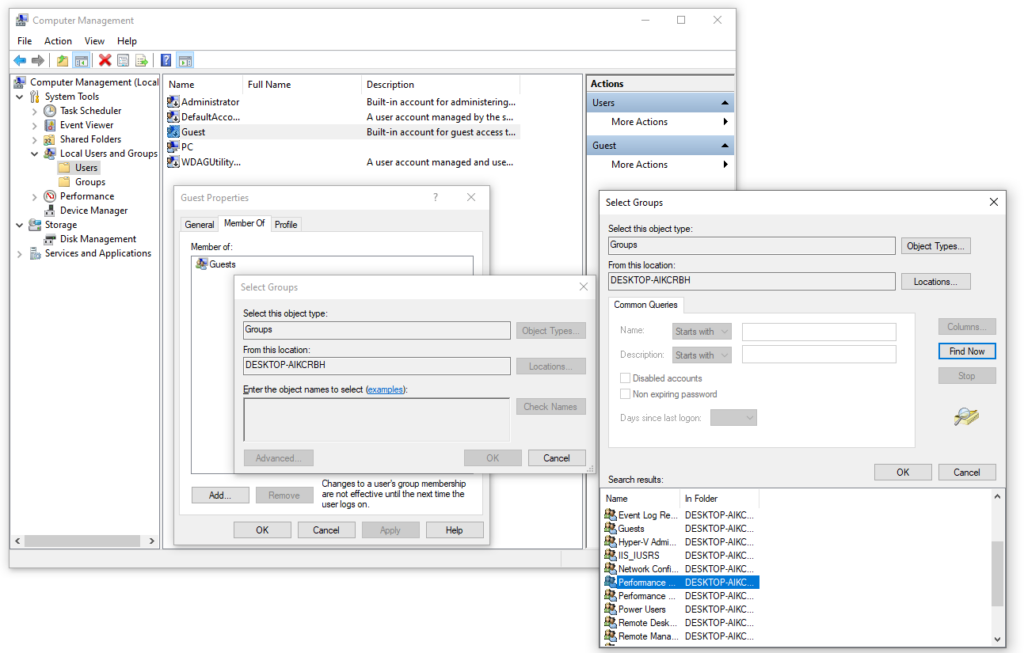
- Add User to Required Groups on the Monitored Server:
- For each monitored server, open Computer Management → Local Users and Groups → Users.
- Double-click the user account you created (e.g.,
DOMAIN\AimBetterUser). - Go to the Member Of tab → Add → Advanced → Find Now.
- Add the following groups:
- Performance Monitor Users
- Performance Log Users
- Click OK to save the group membership.
2. Configure WMI permissions
For both local and remote monitoring, on the monitored server, run wmimgmt.msc to open the Windows Management Instrumentation (WMI) Management Console
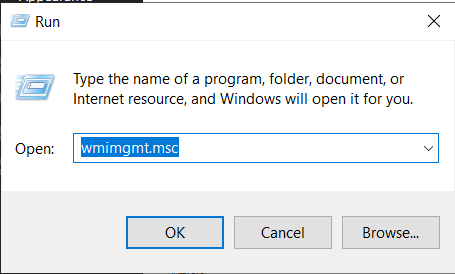
Right-click on WMI Control (Local) and select Properties.
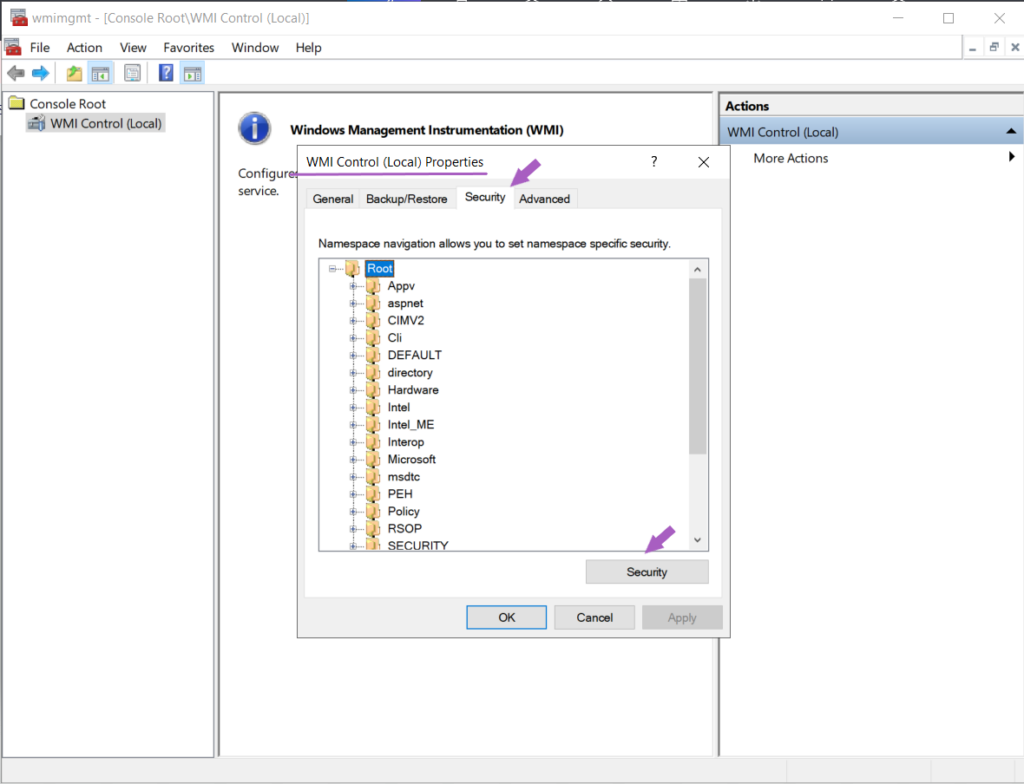
In the Security tab, highlight Root, and click the Security button.
Add the created user and enable the options : Enable Account , Remote Enable , and Read Security Execute Methods
Do the same with CIMV2, adding the created user and enabling the options : Enable Account , Remote Enable , and Read Security Execute Methods
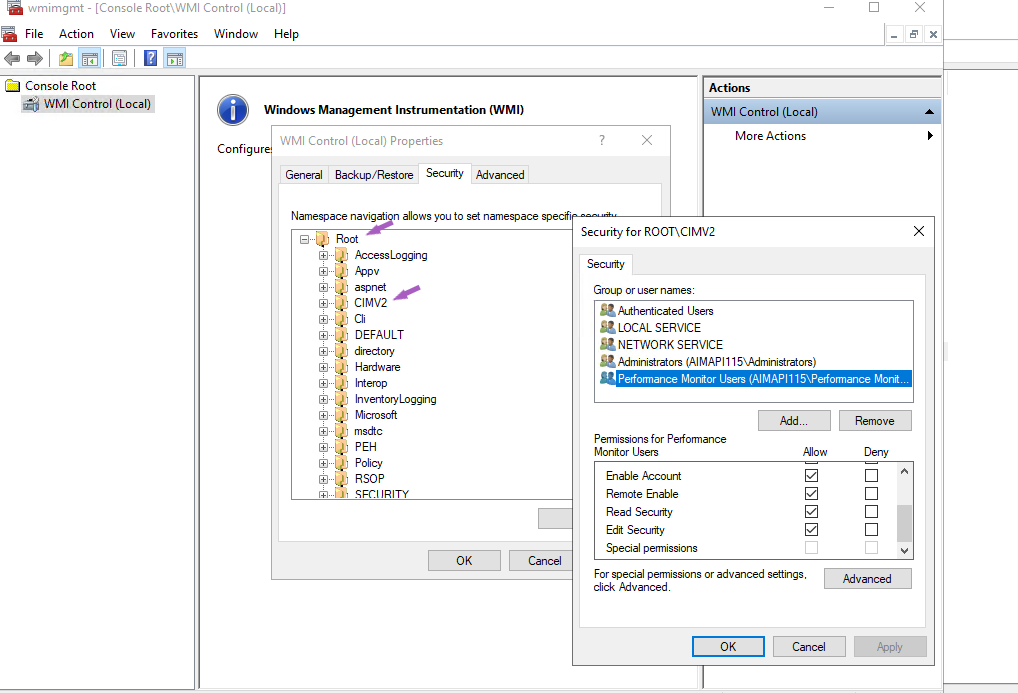
If the “Execute Methods” option is not enabled, the only impact will be if the WMI stops running correctly. In this case, you can manually kill the AimBetter process and restart the WMI.
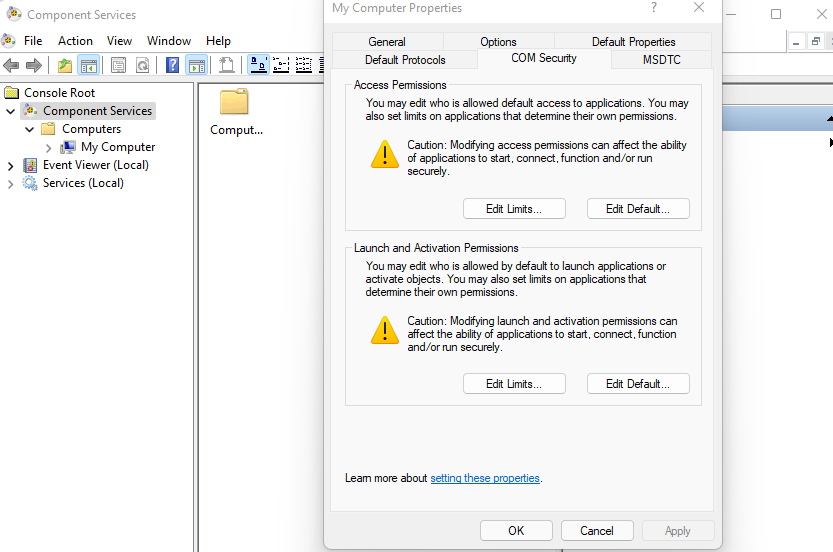
3. Configure COM Security
This configuration is necessary for remote monitoring and should be made on the monitored server.
- Click Start, click Run, type DCOMCNFG, and then click OK.
- In the Component Services dialog box, expand Component Services, expand Computers, right-click My Computer, and click Properties.
- In the My Computer Properties dialog box, click the COM Security tab.
- Under Access Permissions and Launch and Activation Permissions, click Edit Limits.
- Add the user or groups (Performance Monitor Users, Performance Log Users, and Distributed COM Users) and allow remote access, remote launch, and remote activation.
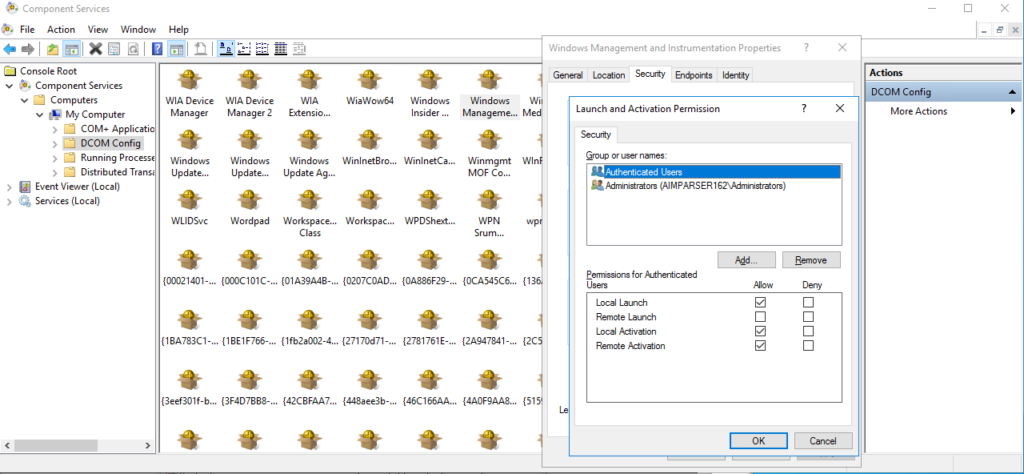
4. Configure DCOM Security
This configuration is necessary for remote monitoring and should be made on the monitored server.
- In the Component Services dialog, double click Computers | My Computer | DCOM Config | Windows Management and Instrumentation.
- Right-click Windows Management and Instrumentation | Properties.
- Click Security | Launch and Activation Permissions | Edit.
- Add the user or groups (Performance Monitor Users, Performance Log Users, and Distributed COM Users).
- Allow Remote Launch and Remote Activation.
- Click OK to close the Launch and Activation Permission dialog and save changes.
- Click OK to close the Windows Management and Instrumentation Properties dialog and save changes.
5. Grant full control over C:\Program Files (x86)\AimBetter folder
The only full control (reading and writing permissions) needed for this user is over the C:\Program Files (x86)\AimBetter folder. This folder is created in the Agent server (where the AimBetter agent is installed).
You may create this folder before the Agent installation and grant full control exclusively over this folder.
6. Access Rights to the C:\PerfLogs Directory on the monitored server
- Write: To create the
Server_Performancefolder and its files. - Read/Modify: To read performance data and update the files.
How to Grant Permissions to C:\PerfLogs
- Open File Explorer and navigate to:
C:\PerfLogs - Right-click the folder → Properties → Security tab
- Click Edit… to modify permissions.
- If the SERVICE principal is not listed:
- Click Add…
- Type
SERVICE→ Check Names → OK - Select SERVICE and grant the following permissions:
- Write → create folders/files
- Read / Modify → read performance data and update files
- Click Apply → OK
- Restart the AimBetter Agent service (or the server, if needed)
7. Firewall requirements
For all installations, configure the Windows Firewall in the Agent Server, where the AimBetter agent is installed, choosing the following apps:
- Performance Logs and Alerts (Domain)
- Windows Management Instrumentation (WMI) (Domain)
- Windows Performance Adapter (Domain, Private and Public)
- Windows Remote Management (Domain, Private, Public)
Read about Firewall configuration on Windows servers – both Agent and Monitored servers.

 +1 (650) 449-8622
+1 (650) 449-8622